How to choose between a risk-based approach and a compliance-based approach? Is it a battle of the titans or a necessary synergy? To put it simply, we could say that the former stems from a "fear of getting hurt" (suffering an attack), while the latter stems from a "fear of the police" (being punished). It's time to take stock of the situation!
1. The compliance approach: mastering the framework
Compliance can fall into three distinct areas:
- Best practices (NIST, ANSSI hygiene guide, etc.);
- Applicable regulations (GDPR, NIS 2, DORA, etc.);
- Certification requirements (ISO 27001, SOC 2, etc.).
The 4-step process
- Identify the regulations or standards to be followed;
- Assess the gap between these and the current situation;
- Implement actions to bridge this gap;
- Maintain compliance over time.
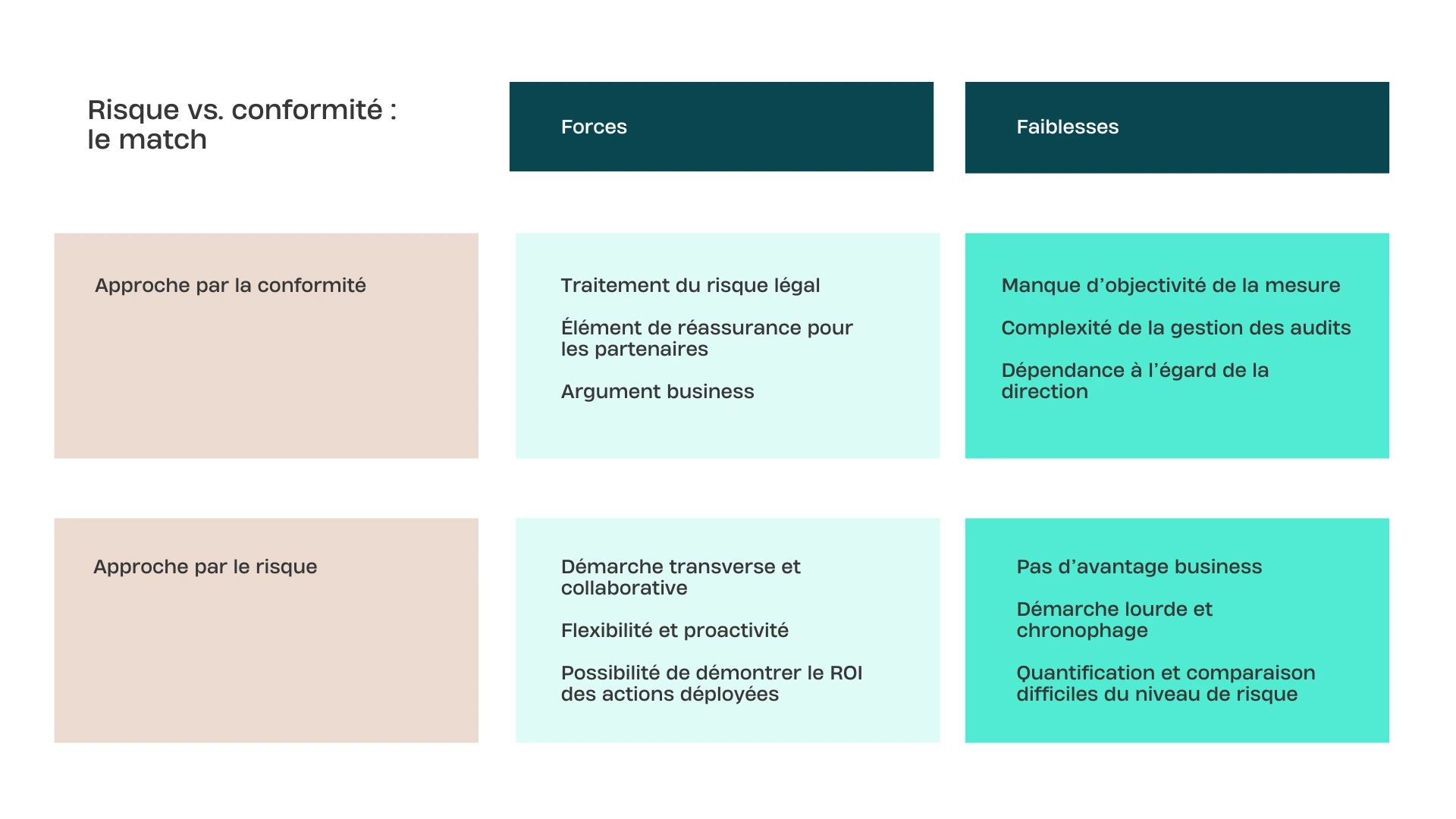
The pros and cons
The advantage: it addresses legal risk and responds to business challenges (calls for tenders).
Limitations: a lack of objectivity at times (self-reported compliance rates), complex audit management, and a heavy reliance on C-level support to enforce measures that are often perceived as rigid.
2. The risk-based approach: operational precision
Adopting a risk-based approach means moving away from checklists and focusing on real threats.
The 4-step process
- Identify a possible incident scenario.
- Analyze the impact on the various stakeholders within the organization.
- Assess the probability (attacker's motivations, current security level).
- Implement corrective actions to mitigate this specific risk.
The pros and cons
The advantage: it is a cross-functional and collaborative approach. It better captures the attention of business units and demonstrates cyber ROI by quantifying the financial impact avoided.
Limitations: it does not always reassure external parties (who prefer a certification logo), and the analysis can be very time-consuming, to the detriment of effective processing.
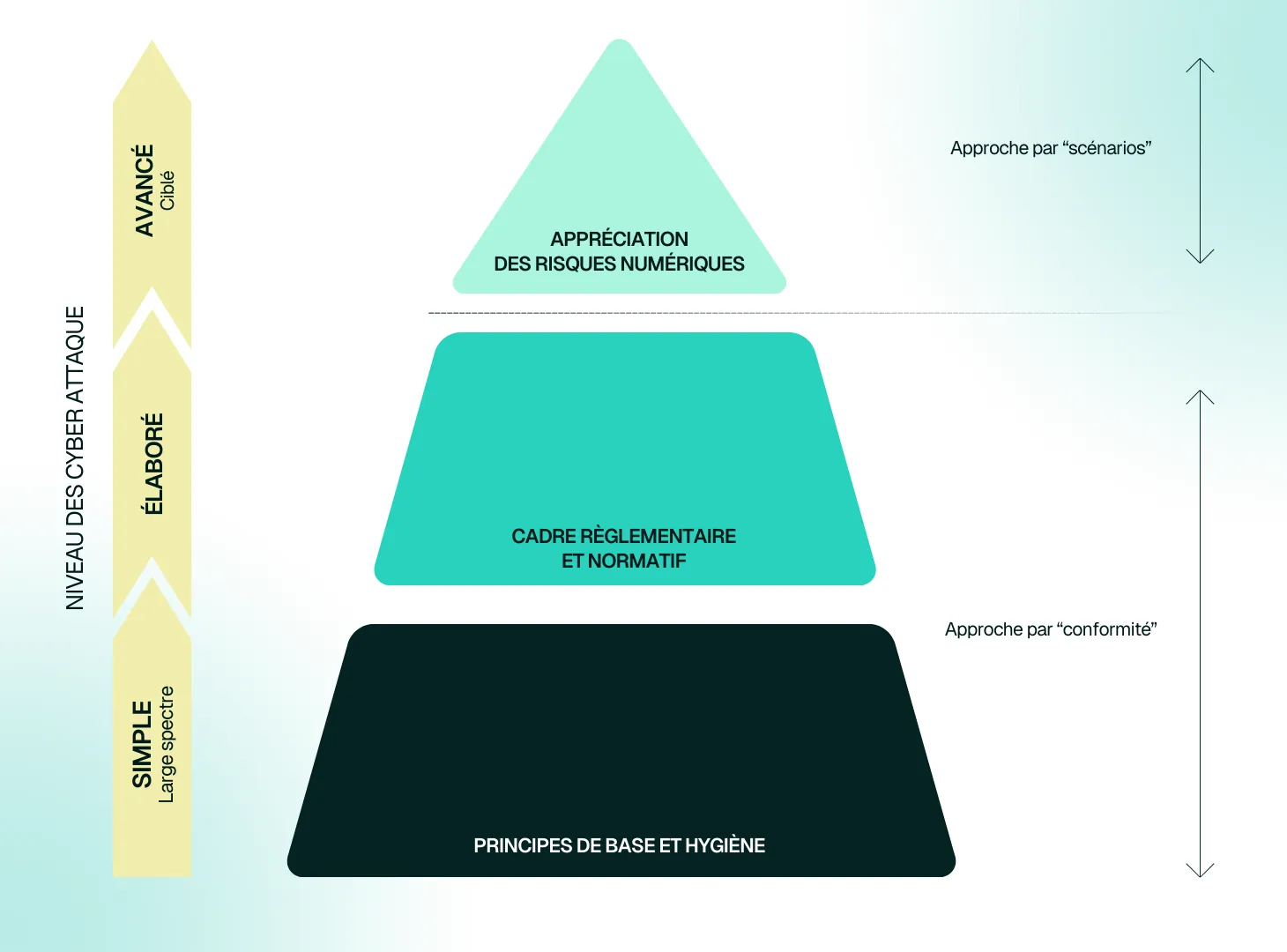
3. The hybrid approach: the sweet spot of cyber management
What if these two approaches were two sides of the same coin? The EBIOS RM pyramid shows us that it is above all a question of timing and maturity.
- The foundation: the compliance approach establishes basic hygiene principles and the legal framework.
- The summit: the risk-based approach refines the strategy for mature organizations.
The Numbers Corner (Tenacy Webinar)
During our dedicated webinar, we asked professionals about their daily lives...
- 58% have adopted the hybrid approach .
- 25% prioritize compliance alone.
- 8% risk alone.
- 8% an "instinctive" approach.
How does Tenacy reconcile risk and compliance?
To avoid having to choose between "fear of the police" and "fear of pain," we need a tool that can unify these two perspectives. Tenacy was designed to offer this traceability and consistency.
- Compliance management: manage your standards and automate evidence collection with our numerous connectors.
- Risk management: identify your scenarios and track your action plans without getting lost in complex Excel files.
- Consolidated view: visualize your overall posture on a single GRC platform.
👉 Discover all of Tenacy's features in the product sheet
FAQ – Your questions about cyber management
Can you be compliant without actually being protected?
Absolutely. That's the trap of "paper" compliance. That's why a risk-based approach is essential to compare theoretical controls with the reality of threats.
How to transition from Excel-based management to automated management?
Thetransition to CRM software allows for the centralization of the knowledge base and facilitates reporting.
Is the hybrid approach more expensive?
Inthe short term, it requires greater involvement. In the long term, it reduces costs by avoiding unnecessary cyber investments and minimizing the financial impact of incidents.
Conclusion: don't choose anymore, combine them
The ultimate goal is a hybrid approach that integrates the compliance foundation while remaining risk-oriented. This is how you will build resilient cybersecurity that is compliant and aligned with business challenges!


.webp)

